เราทำได้มากกว่าพูด
คู่แข่งของเราหลายรายได้ทำการโฆษณาความสามารถที่หลากหลายและอ้างว่าโซลูชัน SD-WAN ของตนเองนั้นทำสิ่งต่างๆ ได้อย่างมากมาย แต่คำกล่าวอ้างเหล่านั้นกลับไม่เป็นไปดังคำโฆษณาเมื่อถึงเวลาที่ต้องทำ Proof of Concept (POC) ในขณะที่เรื่องราวของเรานั้นแตกต่างออกไป ติดต่อเราวันนี้เพื่อทดสอบ Versa Network11 SD-WAN และ SD-Security ได้ทันที เพื่อให้คุณเข้าใจได้อย่างถ่องแท้ว่าผลิตภัณฑ์ของเราสามารถช่วยองค์กรของคุณประหยัดค่าใช้จ่าย, ลดเวลาที่ใช้ในการจัดการ, ลดความซับซ้อนของระบบ และยังช่วยเพิ่มประสิทธิภาพของระบบเครือข่ายคุณได้อย่างไร
ความสามารถของ VERSA NETWORKS
SD-WAN FEATURES
Carrier Grade NAT
Carrier Grade NAT (CGN/CGNAT) หรือที่รู้จักกันในอีกชื่อหนึ่งว่า Large Scale NAT (LSN) นั้นเป็นรูปแบบหนึ่งของการออกแบบระบบเครือข่าย IPv4 ที่ในแต่ละสาขานั้นถูกกำหนดให้ใช้งาน IPv4 แบบ Private ก่อนที่จะถูกแปลงมาเป็น IPv4 แบบสาธารณะ โดยมีอุปกรณ์กลางที่ทำหน้าที่จัดการการแปลง Address เหล่านี้ก่อนออกสู่ Internet ภายนอก กระบวนการนี้ได้ย้ายการทำ Network Address Translation (NAT) ที่เคยอยู่ On-Premises ให้มาอยู่บน Cloud แทน
Stateful Layer 4 Firewall
Firewall นั้นสามารถทำงานได้ที่หลายระดับเมื่ออ้างอิงกับ Open Systems Interconnection (OSI) Model ขึ้นอยู่กับความสามารถในการกรอง Traffic โดยใน Layer 4 Firewall นั้นจะมีการทำงานที่ระดับของ Port Number และจดจำ Source Port และ Destination Port รวมถึงยังมีการตรวจสอบสถานะการเชื่อมต่อและค่า Sequence Number ด้วย การเชื่อมต่อจะเริ่มต้นขึ้นได้จาก Host ภายใน ซึ่งจะถูกจดจำข้อมูลลง State Table หรือ Dynamic Session Table เพื่อให้สามารถติดตามการรับส่งข้อมูลได้ และเฉพาะ Packet ที่ถูกตรวจสอบแล้วว่าตรงกับกฎที่อนุญาตภายใน State Table เท่านั้นที่จะสามารถถูกส่งผ่าน Firewall ไปได้
การทำ Stateful Inspection นี้ช่วยลดการสร้างกฎใหม่ๆ จำนวนมากลงไปได้ โดยสำหรับ Traffic แบบทิศทางเดียวนั้นก็ไม่จำเป็นต้องสร้างกฎที่อนุญาตให้มีการรับส่งข้อมูลจากสองฝ่าย ตัวอย่างเช่น Traffic จากผู้ใช้งานนั้นถูกเริ่มต้นขึ้นในทิศทางเดียวนั้นก็ได้แก่ Telnet (port 23), HTTP (port 80) และ HTTPS (port 443) โดยคอมพิวเตอร์ของผู้ใช้งานเป็นคนเริ่มต้น Traffic ขาออกนี้ ทำให้คุณสามารถสร้างกฎที่อนุญาตให้เกิด Traffic ดังกล่าวนี้สำหรับ Protocol เหล่านี้ได้ ระบบ Stateful Inspection ก็จะทำการอนุญาต Traffic ขากลับที่ตอบสนองต่อ Traffic ขาออกนี้ให้โดยอัตโนมัติ คำว่า Stateful ในที่นี้จึงหมายถึงการที่คุณเพียงแค่ต้องสร้างกฎสำหรับการเริ่มต้น Traffic เท่านั้น ไม่จำเป็นต้องสร้างกฎเพื่อรองรับพฤติกรรมการรับส่งข้อมูลทั้งหมด โดย Packet ที่เป็นส่วนหนึ่งของการเชื่อมต่อที่ได้รับอนุญาตแล้วก็จะถูกประเมินว่าได้รับอนุญาตด้วยทั้งหมดเช่นกัน
Denial of Service
Denial of Service (DoS) คือการโจมตีระบบเครือข่ายชนิดหนึ่ง ที่ถูกออกแบบมาเพื่อทำให้ระบบเครือข่ายหยุดทำงานด้วยการส่ง Traffic ที่ไม่มีประโยชน์ปริมาณมหาศาลเกินกว่าที่ระบบเครือข่ายจะรับได้ การโจมตี DoS หลายๆ รูปแบบนั้นมักมุ่งเน้นไปที่การโจมตีข้อจำกัดที่มีอยู่บน TCP/IP Protocol
แฮ็คเกอร์นั้นจะใช้การโจมตีแบบ DoS เพื่อป้องกันไม่ให้เกิดการใช้งานทรัพยากรคอมพิวเตอร์บนระบบเครือข่ายได้อย่างที่ควรจะเป็น การโจมตีแบบ DoS นี้มีพฤติกรรมร่วมกันคือการทำให้มี Traffic ปริมาณมหาศาลเกิดขึ้นภายในระบบเครือข่าย, ยับยั้งการเชื่อมต่อระหว่างเครื่องคอมพิวเตอร์สองเครื่อง, ป้องกันไม่ให้ผู้ใดผู้หนึ่งเข้าถึงบริการ หรือยับยั้งการให้บริการไปยังระบบหรือผู้ใช้งานใดๆ การโจมตีเหล่านี้อาจเกิดขึ้นกับระบบ Email, Internet หรือ Web Server ก็ได้ โดยการโจมตีแบบ DoS นี้จะทำให้ Bandwidth ที่มีอยู่หมดลง หรือแม้แต่ทำให้ทรัพยากรระบบทั้งหมดอย่างเช่นหน่วยความจำของเครื่อง Server ถูกใช้จนหมด เป็นต้น
Site to Site IP sec VPN
Site to Site IP sec VPN Tunnel นี้ถูกใช้งานเพื่อทำให้เกิดการรับส่งข้อมูล, เสียง และวิดีโอระหว่างสองสาขา (อย่างเช่นออฟฟิศหริอสาขา) ได้อย่างมั่นคงปลอดภัย VPN Tunnel เหล่านี้ถูกสร้างขึ้นมาบน Public Internet และถูกเข้ารหัสด้วยการใช้อัลกอริธึมการเข้ารหัสชั้นสูงอย่างหลากหลาย เพื่อให้มั่นใจว่าข้อมูลจะไม่ถูกสอดส่องในการรับส่งข้อมูลระหว่างสองสาขา.
Site-to-site VPN นี้จะทำการเชื่อมต่อระบบเครือข่ายทั้งหมดเข้าถึงกัน โดยในการทำ Site-to-site VPN นั้น ที่เครื่อง Host จะไม่ต้องมีการติดตั้ง Client Software ใดๆ แต่จะทำการรับส่งข้อมูล TCP/IP ตามปกติไปยัง VPN Gateway แทน และ VPN Gateway ก็จะทำการตอบสนองด้วยการทำ Encapsulation และ Encryption ให้กับข้อมูล Traffic ขาออก ส่งข้อมูลเหล่านั้นไปยัง VPN Tunnel ที่อยู่บน Internet ไปจนถึง VPN Gateway อีกชุดหนึ่งที่สาขาปลายทาง ซึ่งเมื่อ Traffic ดังกล่าวถูกส่งไปถึง VPN Gateway ปลายทางแล้ว ก็จะมีการถอด Header ออก, ถอดรหัสข้อมูลของเนื้อหา และส่งต่อไปยัง Host ปลายทางใน Private Network นั้นๆ
Dynamic IPSec Overlay
Dynamic IPSEC VPN Overlay คือการสร้าง Dynamic IPSEC Tunnel ระหว่างสองสาขา โดยเมื่อคุณเชื่อมต่อสองสาขาเข้ากับ Controller เรียบร้อยแล้ว Controller ก็จะทำหน้าที่เป็น Route-Reflector Client ที่แลกเปลี่ยนข้อมูลอย่างเช่น IPSEC-SA, L3VPN และอื่นๆ ระหว่างสาขาหนึ่งๆ ไปยังสาขาอื่น โดยเมื่อ IPSEC-SA ถูกส่งไปถึงปลายทางแล้ว สาขาต่างๆ ก็จะเริ่มสร้าง Dynamic IPSEC เชื่อมต่อไปยังสาขาอื่นๆ ซึ่งนี่เองก็เป็นวิธีการที่การสื่อสารระหว่างสาขาจะเกิดขึ้นผ่าน IPSEC Tunnel ได้
Traffic Load Balancing
เรามีความสามารถชั้นสูงในการทำ Layer 4 (L4) Load Balancing (LB) อยู่มากมาย ซึ่งโดยมากแล้วจะอ้างอิงกับ IP Address และ Port ของ Source และ Destination ที่ถูกบันทึกเอาไว้ใน Packet Header
เทคโนโลยี Load Balancing (LB) ของเรานั้นจะมีการสร้าง Virtual IP Address (VIP) ขึ้นมา และทำการแปลงค่าระหว่าง VIP และ Real IP Address ด้วยการทำ Mux/Demux ระหว่าง Server หรือเครือข่ายปลายทางด้วยการใช้ Translation Table ซึ่งเบื้องหลังนั้นจะมีการรองรับอัลกอริธึมในการทำ Load Balancing ที่หลากหลาย (ได้แก่ RR/WRR, Source/Destination Hash, Least Connection และอื่นๆ) และยังรองรับการทำ Health Monitoring สำหรับ UDP และ TCP และเทคนิคการทำ Source และ/หรือ Destination IP Address Persistence ด้วย ความสามารถเหล่านี้ทำให้โซลูชัน NaaS สามารถนำบริการต่างๆ มาเรียงต่อกันเพื่อควบคุมเส้นทางการรับส่งข้อมูลและกำหนดลำดับการให้บริการได้ตามต้องการได้ไม่ว่าจะเป็นระบบแบบ Physical หรือ Logical จากผู้พัฒนาเทคโนโลยีรายอื่นๆ ก็ตาม
การมองเห็นถึงระดับ Application (Visibility)
ถึงแม้หมายเลข Port, Protocol และ IP Address นั้นจะเป็นสิ่งที่มีประโยชน์ต่ออุปกรณ์เครือข่าย แต่ข้อมูลเหล่านี้ก็ทำให้เรารู้จักระบบเครือข่ายของลูกค้าได้เพียงเล็กน้อยเท่านั้น ข้อมูลรายละเอียดเชิงลึกเกี่ยวกับ Application, ผู้ใช้งาน และเนื้อหาที่มีอยู่ในเครือข่ายนั้นช่วยให้เราสามารถวิเคราะห์ความเสี่ยงและตอบสนองได้อย่างแม่นยำ
Application Traffic Management, SLAs, Application Shaping and QoS
การทำ Policy Based Traffic Forwarding (PBF) สำหรับ Application, การทำ Traffic Engineering (TE) สำหรับ Application และการกำหนด Quality of Service (QoS) สำหรับ Application นั้นคือชุดความสามารถด้านการบริหารจัดการ Traffic ที่มีให้ใช้งานได้บนโซลูชัน Versa Network 11 SD-WAN
ด้วยการใช้งาน App-QoS กลุ่มความสามารถด้าน QoS นั้นก็สามารถถูกใช้เพื่อควบคุมการทำงานของ Application ได้ ไม่ว่าจะเป็นการทำ Marking, Rate Limiting, Prioritization, Drop Profile Assignment & Management, Adaptive Shaping, Hierarchical Queuing และอื่นๆ เพื่อช่วยให้สามารถบริหารจัดการและกำหนดลำดับความสำคัญของลิงค์และเส้นทางที่ดีที่สุดตามลำดับความสำคัญของ Application ได้ ทำให้มีแบนด์วิดธ์สำหรับ Application ที่มากขึ้นและตอบโจทย์ด้าน SLA ได้ดียิ่งขึ้น
ในขณะที่การใช้งาน App-PBF การบริหารจัดการการใช้งาน Application ของผู้ใช้งานนั้นจะอ้างอิงกับการตรวจสอบนโยบายและเงื่อนไขต่างๆ เพื่อควบคุมให้การทำงานเป็นไปตามนโยบายที่กำหนดเป็นหลัก ได้แก่ การ Forward, การ Forward to Service Chain และการบังคับใช้ Security Profile ที่มีการกำหนด Nexthop Override Function และอื่นๆ อีกมากมายได้
ส่วนการใช้ App-TE นั้นจะเป็นการใช้ความสามารถด้านการบริหารจัดการการรับส่งข้อมูลของ Application โดยอ้างอิงจากลิงค์, เส้นทางการเชื่อมต่อ, ประสิทธิภาพของการรับส่งข้อมูล, Delay, Jitter และพฤติกรรมการเกิด Packet Loss ที่เปลี่ยนแปลงอย่างต่อเนื่องเป็นหลัก ความสามารถในการทำ App-TE/App-SLA Management นี้จะทำให้ผู้ให้บริการระบบเครือข่ายสามารถให้บริการ Application ต่างๆ ได้ดีที่สุดตามปัจจัยบนระบบเครือข่ายที่เปลี่ยนแปลงอย่างต่อเนื่อง
Migration Gateway
เพื่อเปลี่ยนให้ระบบเครือข่ายเดิมของลูกค้ากลายเป็นระบบเครือข่ายแบบ SD-WAN ได้ ลูกค้าของเราจำเป็นต้องมี Migration Gateway ที่จะช่วยให้สามารถแปลงข้อมูลใน Packet และแลกเปลี่ยนข้อมูลความสำเร็จในการรับส่งข้อมูลระหว่าง Protocol ที่แตกต่างกันได้ รวมถึงยังมีข้อมูลเพื่อใช้ในการติดตามการทำงานและการระบุประเภทของข้อมูล Application ไปจนถึงการเปลี่ยนสลับเส้นทางการรับส่งข้อมูลระหว่างระบบเครือข่ายที่มีอยู่เดิมและระบบ SD-WAN
การเพิ่มระบบ SD-WAN เข้าไปยังระบบ WAN ที่มีอยู่เดิมนั้นสามารถทำได้อย่างง่ายดาย โดยในระหว่างที่มีการย้ายระบบนั้น อุปกรณ์ WAN, บริการ และการเชื่อมต่อที่เกิดขึ้นอยู่นั้นก็จะยังคงทำงานเหมือนเดิมต่อไป และเมื่อสบโอกาสที่จะสามารถทำงานทดแทนระบบ WAN ที่มีอยู่เดิมได้แล้ว การสร้าง Virtual WAN Overlay นั้นก็ไม่ต้องมีการอัปเกรดครั้งใหญ่ของระบบ Router หรือโครงสร้างพื้นฐานเดิมขึ้นมาแต่อย่างใด หรือเรียกง่ายๆ ว่า ลูกค้าของเราสามารถเริ่มต้นย้ายระบบได้ทันทีที่ต้องการ โดยไม่ต้องหยุดการทำงานของระบบใดๆ นั่นเอง
Multiple Active Links
Versa Network11 สามารถมีลิงค์ที่ทำงานพร้อมกันได้หลายลิงค์แบบ Active/Active ไม่ว่าจะเป็นลิงค์แบบบรอดแบนด์, 4G-LTE, MPLS หรือ IPSEC Tunnel ก็ตาม แนวทางการทำงานแบบ Active-Active นี้จะอ้างอิงกับประสิทธิภาพของลิงค์เพื่อไม่ให้เกิดกรณีที่ระบบเครือข่ายขาดไปทั้งหมดหรือขาดไปชั่วคราวแม้เพียงเสี้ยววินาที การมีลิงค์และผู้ให้บริการที่หลากหลายนี้จะช่วยให้ระบบมีความมั่นคงทนทานสูงขึ้น
Inline Loss Management
Versa Network11 จะยังคงส่งข้อมูล SLA PDU ระหว่างลิงค์ WAN ในแต่ละสาขา ตัวอย่างเช่น หากการเชื่อมต่อระหว่างสองสาขานั้นมี WAN ด้วยกันสองลิงค์ ในทุกๆ ช่วงเวลาที่กำหนดไว้ ระบบของเราจะทำการส่ง SLA PDU ระหว่าง WAN เหล่านี้ และทำการวิเคราะห์จากข้อมูลที่ได้รับว่าเกิด Loss, Delay, Jitter มากน้อยเพียงใดระหว่างสาขา ข้อมูลเหล่านี้เรียกว่า SLA Paramenter เราจะพิจารณาค่า SLA PDU นี้และข้อมูล Packet เพื่อวิเคราะห์อัตราส่วนของการเกิดข้อมูลสูญหายระหว่างสองสาขานี้ และเรายังมีการคำนวนอัตราส่วนนี้จากการรับส่งข้อมูลจริงที่เรียกว่า Inline Loss Management อีกด้วย โดยอ้างอิงจากข้อมูลเหล่านี้ เราก็จะสามารถเลือกได้อย่างแม่นยำว่าควรรับส่งข้อมูลผ่าน WAN ใด
Packet Striping
Versa Networks สามารถช่วยให้ลิงค์ที่มีความเร็วเท่ากันของลูกค้าทำงานร่วมกันได้ ทำให้โซลูชัน SD-WAN สามารถใช้แบนด์วิดธ์ได้สูงขึ้นจากการนำความเร็วของแต่ละลิงค์มารวมกัน ความสามารถนี้เป็นสิ่งที่จำเป็นสำหรับสาขาที่มีลิงค์หรือเส้นทางการรับส่งข้อมูลที่มีความเร็วน้อยจำนวนมาก
Versa Network11 จะทำ Load Balancing สำหรับแต่ละชุดของการรับส่งข้อมูล ซึ่งแนวทางนี้สามารถตอบโจทย์การใช้งานจริงได้มากกว่า 90% โดยในกรณีที่เรียกว่า “Elephant Flows” การทำ Load Balancing ในลักษณะนี้จะทำให้บางลิงค์ถูกใช้งานสูงจนเกือบเต็มหรือสูงมากเกินไปสำหรับลิงค์ที่มีความเร็วต่ำ ในขณะที่ลิงค์ที่เหลือนั้นอาจไม่ได้ถูกใช้งานเท่าที่ควร
เพื่อแก้ไขปัญหานี้ Versan Network11 ก็ยังมีความสามารถในการทำ Load Balance ที่ระดับ Packet กระจายไปยังหลายลิงค์หรือหลายเส้นทางได้ ซึ่งเมื่อเปิดใช้งานความสามารถนี้แล้ว Packet ในการรับส่งข้อมูลที่เกี่ยวข้องกันนั้นก็จะถูกกระจายไปยังหลายเส้นทาง โดยมีการกำหนด Sequence Number เอาไว้บนแต่ละ Packet วิธีการนี้จะช่วยให้ลิงค์ทั้งหมดสามารถถูกใช้งานรวมกันได้ และในฝั่งที่เป็นผู้รับข้อมูลนั้นก็จะนำ Sequence Number ของแต่ละ Packet มาใช้เพื่อให้มั่นใจว่าลำดับของข้อมูลจะยังคงถูกต้อง และถูกส่งต่อไปยังปลายทางได้อย่างแม่นยำ
Forward Error Correcting (FEC)
เทคโนโลยี Forward Error Correction (FEC) ใน SD-WAN ของ Versa Network11 สามารถสร้าง Packet ที่ตกหล่นไปขึ้นมาใหม่ได้โดยรองรับการสูญหายของข้อมูลถึง 25% ด้วยการเพิ่ม Loss-Recovery Packet ที่มี Signature อยู่ภายในเข้าไปทุกๆ 4 Packet ที่ถูกส่งออกไป ดังนั้นหากมี Packet ใดที่สูญหายไป ก็จะสามารถสร้าง Packet นั้นๆ ขึ้นมาใหม่ได้จากข้อมูล Signature ดังกล่าวนั่นเอง วิธีการนี้จะช่วยลดการเกิด Packet Retransmission ลงได้ และยังช่วยลด Latency ให้น้อยลง ส่งผลให้ประสบการณ์ของผู้ใช้งานนั้นดีขึ้น.
Forward Error Correction (FEC) คือเทคนิคในการประมวลผลข้อมูล Digital เพื่อช่วยเพิ่มความมั่นคงทนทานของข้อมูล โดยการใช้แนวคิดของ Redundant Data ที่เรียกว่า Error Correcting Code ที่ถูกสร้างขึ้นมาก่อนที่จะมีการส่งหรือบันทึกข้อมูล FEC จะช่วยให้ฝั่งผู้รับข้อมูลนั้นสามารถแก้ไขความผิดพลาดที่เกิดขึ้นใหม่ได้โดยไม่ต้องมีการสื่อสารกลับไปยังต้นทางเพื่อร้องขอข้อมูลในส่วนที่สูญหาย
หัวใจหลักของแนวทางนี้ก็คือการที่ผู้ส่งขจ้อมูลนั้นต้องทำการ Encode เนื้อหาแบบ Redundant ด้วยการใช้ Error Correcting Code (ECC) เพื่อให้ฝั่งผู้รับนั้นสามารถตรวจสอบความผิดพลาดในระดับหนึ่งได้ด้วยตนเองและยังสามารถซ่อมแซมข้อมูลส่วนที่สูญหายไปได้โดยไม่ต้องร้องข้อข้อมูลซ้ำ FEC นั้นจะทำให้ผู้รับข้อมูลสามารถซ่อมแซมข้อมูลได้ด้วยตนเองโดยไม่ต้องมีการ้องขอข้อมูลซ้ำ แต่ก็มาพร้อมกับจุดอ่อนก็คือการที่จะต้องใช้ Bandwidth ที่สูงขึ้นนั่นเอง ดังนั้น FEC จึงเหมาะกับสถานการณ์ที่ไม่สามารถยอมให้เกิดการร้องขอเพื่อส่งข้อมูลซ้ำได้ อย่างเช่นการสื่อสารแบบทางเดียว และเมื่อการส่งข้อมูลนั้นเป็นการส่งข้อมูลไปยังผู้รับหลายคนพร้อมกันด้วยการทำ Multicast
Packet Cloning
ไม่ว่าการที่คุณภาพในการรับส่งข้อมูลจะลดลงจากการที่เกิดการสูญหายของ Packet หรือจะเกิดจากประเด็นด้านความมั่นคงทนทานของระบบเครือข่ายที่ใช้งานก็ตาม Versa Network11 SD-WAN ก็ยังสามารถทำให้มั่นใจได้ว่าการส่งข้อมูลนั้นๆ จะไปถึงปลายทางได้อย่างครบถ้วน ด้วยการทำ Packet Cloning ที่จะทำการสำเนาข้อมูลชุดเดียวกันและส่งไปยัง Link ทั้งหมดที่มีพร้อมๆ กันเพื่อให้มั่นใจว่า SD-WAN Node ปลายทางจะได้รับข้อมูลอย่างแน่นอน ถึงแม้ข้อมูลบางส่วนจะสูญหายไปบ้างก็ตาม โดยเมื่อ Packet เหล่านั้นถูกส่งไปถึงผู้รับและถูกจัดเรียงตามลำดับแล้ว ข้อมูลที่ถูกสำเนาก็จะถูกกำจัดทิ้งโดยอัตโนมัติ เทคนิคนี้เหมาะกับระบบ VoIP ที่ข้อมูลเสียงนั้นมักมีขนาดไม่ใหญ่มากนัก
SD-SECURITY FEATURES
Next Generation Firewall & Unified Threat Management
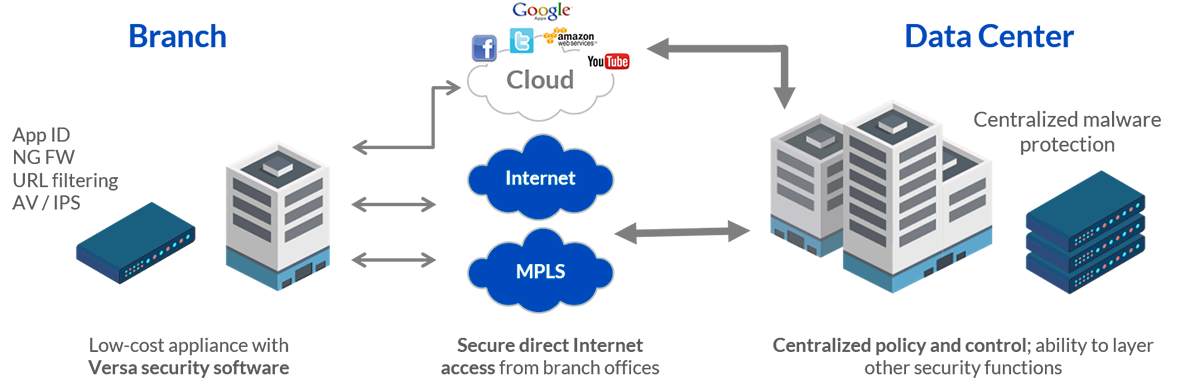
จุดอ่อนที่สำคัญที่สุดของธุรกิจองค์กรนั้นก็คือออฟฟิศสาขา ที่มักไม่มีเจ้าหน้าที่ฝ่าย IT ประจำอยู่และต้องใช้ช่องทางการสื่อสารที่หลากหลาย (เช่น Internet สำหรับธุรกิจ, บรอดแบนด์, MPLS, Ethernet, LTE และอื่นๆ) ทำให้การผสานผลิตภัณฑ์ด้านระบบเครือข่ายและความมั่นคงปลอดภัยในหลายสาขานี้เป็นไปได้อย่างยากเย็น
Gartner ได้ประมาณการณ์เอาไว้ว่า 30% ของภัยคุกคามขั้นสูงนั้นจะมุ่งเป้าโจมตีไปยังสาขาของธุรกิจเหล่านี้
ความสามารถด้าน Security แบบ Software-based จะช่วยเพิ่มความมั่นคงปลอดภัยให้กับสาขาและช่วยให้การบริหารจัดการนั้นง่ายดายยิ่งขึ้น โดยสามารถแก้ไขปัญหาใหญ่ด้านความมั่นคงปลอดภัยได้ถึง 2 ประการด้วยกัน ได้แก่การมีเจ้าหน้าที่ด้าน IT ที่จำกัด และการผสานระบบเครือข่ายอย่างซับซ้อน แนวทางแบบ Software-Defined สำหรับระบบรักษาความมั่นคงปลอดภัยนี้ได้ใช้แนวทางในการทำ Virtualized Network และ Function ต่างๆ ให้ทำงานได้บน Hardware ทั่วๆ ไป
โซลูชันด้านความมั่นคงปลอดภัยแบบ Software-based ของ Versa Network11 จะช่วยให้คุณสามารถใช้งานความสามารถได้หลากหลาย, เพิ่มความคุ้มค่าในการลงทุนให้สูงสุด และช่วยปรับให้การทำงานนั้นง่ายนดายยิ่งขึ้นสำหรับลูกค้าของคุณด้วยแนวทางการทำ Zero-touch Provisioning และการทำ Automatic Service Chaining
Next-Generation Firewall (NGFW)
Firewall นั้นคือเสาหลักทางด้าน Network Security และความสามารถพื้นฐานที่สุดนั้นก็คือการควบคุม Traffic ที่เกิดขึ้นระหว่างระบบเครือข่ายที่ไว้ใจได้ เช่น ระบบ LAN ขององค์กร กับระบบเครือข่ายสาธารณะที่ไม่น่าไว้ใจ เช่น Internet โดยจากแนวโน้มการเพิ่มขึ้นของระบบ Application ในระบบเครือข่ายที่เติบโตอย่างรวดเร็ว, ประเด็นด้านภัยคุกคามต่างๆ และการทำ Compliance ที่เข้ามามีบทบาทเป็นอย่างมากในการออกแบบความมั่นคงปลอดภัยให้กับระบบเครือข่าย ความต้องการในการใช้งานของระบบ Firewall นั้นจึงสูงขึ้นอย่างไม่เคยเป็นมาก่อน
โซลูชัน Versa Network11 Next-Generation Firewall (NGFW) นี้ได้ผสานรวมเอาความสามารถในการทำ Application Awareness, การผสานระบบเข้ากับ User Role และการทำ Deep Packet Inspection (DPI) เพื่อให้ลูกค้าสามารถควบคุมการใช้งาน Application ของผู้ใช้งานและระบบโครงสร้างพื้นฐานทางด้านเครือข่ายได้ NGFW สามารถควบคุมการเชื่อมต่อเครือข่ายตามนโยบายที่กำหนดได้อย่างละเอียดด้วยปัจจัยต่างๆ เช่น User ID, Application, URL Category, Group Membership และเวลาที่เชื่อมต่อเครือข่าย เป็นต้น Application Level Gateways (ALG) ก็เป็นอีกความสามารถหนึ่งที่รองรับการใช้งานได้ร่วมกับหลาย Protocol เพื่อให้มั่นใจว่าการทำ Firewall และ Network Address Translation (NAT) นี้จะสามารถใช้งานได้กับทุกๆ Application
URL Categorization, Filtering and Control
โซลูชัน Virtual Customer Premise Equipment (vCPE) และ SD-Security นี้มีความสามารถด้าน URL Categorization และ Filtering Capabilities ที่หลากหลายเพื่อกรองข้อมูล Traffic การเข้าถึงเว็บต่างๆ และช่วยลดความเสี่ยงหรือตอบโจทย์ด้านการทำ Compliance ตามนโยบายขององค์กรได้เป็นอย่างดี รวมถึงยังทำการควบคุมเนื้อหาสำหรับเด็กได้ และยังรองรับการยืนยันตัวตนและกำหนดสิทธิ์ในการเข้าถึงเนื้อหาต่างๆ ไปจนถึงยังสามารถออกแบบระบบให้ทำงานได้ตามต้องการ
โซลูชันนี้มี URL Category ให้พร้อมใช้งานได้มากกว่า 80 รายการ เพื่อให้ลูกค้าสามารถบริหารจัดการ URL ได้ตามหมวดหมู่, ความน่าเชื่อถือ, ความมั่นใจ และอื่นๆ อีกทั้ง Versa Network11 ก็ยังเปิดให้สามารถกำหนดหมวดหมู่เองเพิ่มเติมได้อย่างอิสระเพื่อให้ตอบโจทย์ต่อการใช้งานในแต่ละธุรกิจได้
ความสามารถเหล่านี้ถือเป็นหัวใจสำคัญในการให้บริการเครือข่ายแก่ธุรกิจองค์กรได้อย่างปลอดภัยและตรงตามข้อกำหนด ด้วยความสามารถที่เปิดให้ควบคุมผู้ใช้งานได้ระดับราย User หรือ User Group ก็ทำให้สามารถควบคุมพฤติกรรมการเข้าถึง URL ให้แตกต่างกันไปตามแต่ละกลุ่มผู้ใช้งานได้ เช่น การ Allow, Alert, Drop Session/Packet, Reject, Ask, Justify, Block ไปจนถึงการ Override
L7 Access Control
ความสามารถ Application Access Control จะช่วยให้สามารถบริหารจัดการและรักษาความมั่นคงปลอดภัยให้กับ Traffic ของ Application ด้วยการบังคับใช้ Policy ที่หลากหลาย โซลูชันของ Versa Network11 สามารถจำแนกข้อมูล Traffic ของ Application ได้มากกว่า 2,600 รายการ และจัดกลุ่ม Traffic เหล่านั้นเพื่อให้ง่ายต่อการบริหารจัดการแต่ละ Application ได้
การทำ Application Access Control นี้จะรองรับทั้งการ Allo, Deny, Restrict Access, Redirection, การทำ Captive Portal ก่อนเข้าถึง Application, การเก็บ Log ไปจนถึงความสามารถขั้นสูงอย่างเช่นการทำ Scripting โดยเมื่อผสานความสามารถเหล่านี้เข้ากับการทำ User/Group Level Access Control ก็ทำให้ความสามารถ Application Access Control นั้นเป็นความสามารถในการควบคุมการใช้งานระบบเครือข่ายที่ทรงพลังเป็นอย่างมากสำหรับผู้ให้บริการเครือข่าย
URL & IP Reputation Feeds
NGFW นี้ยังได้รวมเอาโซลูชันด้าน URL และ IP Reputation ชั้นนำเอาไว้ด้วยเพื่อให้สามารถบริหารจัดการ Traffic ตาม URL หรือ IP ได้อย่างมีประสิทธิภาพจากการรวบรวมข้อมูลจากผผู้ใช้งานทั่วโลกอย่างเป็นระบบ
เมื่อใช้ความสามารถนี้ร่วมกับการทำ URL Filtering ความสามารถดังกล่าวก็จะช่วยให้มั่นใจได้ว่า Traffic ที่เกิดขึ้นจะไม่มีการเชื่อมต่อไปยังเว็บไซต์ที่น่าสงสัยหรือไม่ผ่าน Compliance อย่างแน่นอนจากประสบการณ์ของผู้ใช้งานที่ได้ทำการรวบรวมมา โดย URL & IP Reputation Feed นี้จะถูกอัปเดตอย่างต่อเนื่องเป็นประจำเพื่อให้สะท้อนถึงการเปลี่ยนแปลงของ Internet และผู้ใช้งานที่เกิดขึ้นจริง ทำให้ความสามารถนี้สามารถตอบโจทย์ด้านการยับยั้ง Traffic ที่เป็น C&C Virus หรือ Malware ซึ่งสามารถฝังตัวเข้าไปยังเครื่องคอมพิวเตอร์ของผู้ใช้งานหรือเนื้อหาต่างๆ ได้เป็นอย่างดี
User/Group Access Control
โซลูชัน Versa Network11 NaaS นี้ยังมีความสามารถ User & Group Based Control มาให้พร้อมใช้งานได้ทันที ทำให้สามารถรักษาความมั่นคงปลอดภัยหรือบังคับใช้นโยบายต่างๆ ได้ตามการยืนยันตัวตนระดับผู้ใช้งานหรือกลุ่มได้ โซลูชัน NaaS นี้สามารถทำงานร่วมกับ Active Directory ได้ผ่านทาง LDAP และ Kerberos ทำให้สามารถเข้าถึงข้อมูลของ User หรือ Group เพื่อบังคับด้านความมั่นคงปลอดภัยหรือการเข้าถึงได้ทันที
การควบคุมนโยบายและความมั่นคงปลอดภัยในระดับ User และ Group นี้ยังช่วยให้สามารถสร้างหรือระงับบางบริการสำหรับ User หรือ Group ได้ เช่น การควบคุมเนื้อหาสำหรับเด็กตามคำแนะนำของผู้ปกครอง, การบังคับให้ทำตาม Compliance, การกำหนดนโยบายการเข้าถึงหรือสิทธิ์ต่างๆ และการสร้างนโยบายเฉพาะขึ้นมาสำหรับผู้ใช้งานแต่ละกลุ่ม เช่น ผู้บริหารระดับสูง, แขกชั่วคราว, พนักงานชั่วคราว และอื่นๆ
ด้วยนโยบายที่มีมิตินี้ SD-Security และ SD-WAN ก็สามารถตอบโจทย์ของวงการที่ต้องการทำนโนบายซึ่งมีการตัดสินใจที่ซับซ้อนได้ เช่น การทำ Routing Policy, การกำหนด Application Policy, การใช้งาน URL & IP Reputation ร่วมกับข้อมูล User & Group ซึ่งทั้งหมดนี้จะช่วยให้การสร้างนโยบายที่ทรงพลังเพื่อควบคุม Traffic ของผู้ใช้งานโดยตรงนั้นเป็นจริงขึ้นมาได้
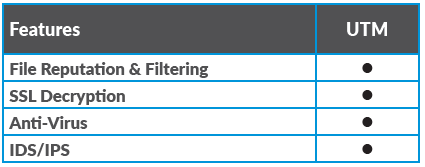
Unified Threat Management (UTM)
Unified Threat Management (UTM) สามารถช่วยเพิ่มการรับรู้และการควบคุมด้านความมั่นคงปลอดภัยและแนวโน้มต่างๆ ที่อาจกลายเป็นปัญหาในอนาคตซึ่งเกี่ยวข้องกับ Traffic ในระบบเครือข่าย, พฤติกรรมของผู้ใช้งาน และเนื้อหาภายใน Application ได้ อีกทั้งยังช่วยเพิ่มความสามารถในการตรวจจับภัยคุกคามด้านความมั่นคงปลอดภัยได้ด้วยการรองรับเทคโนโลยีการตรวจจับภัยคุกคามและการป้องกันชั้นสูงมากกว่าความสามารถของ Firewall ทั่วไปได้เข้ามา
UTM เมื่อใช้งานร่วมกับ SD-WAN และ Next Generation Firewall (NGFW) แล้ว ก็จะทำให้ลูกค้ามองเห็นและควบคุมความมั่นคงปลอดภัยบนระบบเครือข่ายได้มากขึ้น และยังช่วยให้การดูแลรักษาจัดการระบบเครือข่ายง่ายดายขึ้นอีกด้วย
โซลูชัน Versa Network11 UTM นี้ได้รวมเอาการทำ Application Control, IDS/IPS, Web Filtering, Antivirus, Antispam, File Filtering, SSL Decryption และความสามารถชั้นสูงด้านความมั่นคงปลอดภัยอื่นๆ เข้าไว้เพื่อให้ลูกค้าสามารถให้บริการด้านความมั่นคงปลอดภภัยในระดับสูงได้
Anti-Virus Protection
ภายในโซลูชันของ Versa Network11 UTM เรายังได้มีความสามารถด้าน Antivirus มากมายนมาให้พร้อมใช้งานด้วยการใช้เทคนิคแบบ Multilayered ได้แก่ Heuristics, Signature Mathing และ Emulation โดยโซลูชันด้าน Antivirus ของเราใช้ CPU และหน่วยความจำที่น้อย ทำให้ใช้งานทรัพยากรที่มีได้อย่างคุ้มค่า ส่งผลให้การลงทุนคุ้มค่าไปด้วย และ Signature ของ Antivirus นี้ก็ยังได้รับการอัปเดตอย่างสม่ำเสมอ โดยรวมไปถึงการอัปเดต FlexVNF Instance ด้วย ทำให้ผู้ใช้งานนั้นได้ใช้งาน Virus Signature ล่าสุดอยู่ตลอด และปกป้องระบบเครือข่ายของลูกค้าได้อย่างมีประสิทธิภาพมากขึ้น
Intrusion Detection & Intrusion Protection
โซลูชัน Intrusion Detection System (IDS) และ Intrusion Protection System (IPS) นี้ถือเป็นส่วนหนึ่งของ UTM ที่จะทำให้ลูกค้าสามารถตรวจสอบระบบเครือข่ายของตนเองเพื่อค้นหาพฤติกรรมอันตรายหรือการละเมิดนโยบายที่กำหนดเอาไว้ได้ ไม่ว่าพฤติกรรมนั้นๆ จะมีต้นตออยู่ภายในหรือภายนอกระบบเครือข่ายก็ตาม ความสามารถด้าน IDS/IPS นี้ครอบคลุมทั้งการตรวจจับ, การยับยั้ง, การบันทึกข้อมูล Log และการออกรายงาน ไปจนถึงการทำหน้าที่เป็นเครื่องมือในการตรวจจับการละเมิด Compliance ของ User และ Application ต่างๆ ได้ด้วย
โซลูชัน Versa Network11 IDS/IPS นี้มี Profile การโจมตีที่หลากหลายมาให้พร้อมใช้งานเพื่อรองรับการตรวจจับการโจมตีที่จะเกิดขึ้นกับ OS, Server และ Client ได้หลากหลาย ซึ่งเมื่อเปิดใช้งานแล้ว IDS/IPS จะเริ่มต้นใช้งาน Pattern Matching Algorithm เพื่อตรวจจับและยังยั้งการโจมตีทันที ทำให้มั่นใจได้ว่าข้อมูลสำคัญและระบบเครือข่ายจะได้รับการปกป้องอย่างแน่นอน
SSL & TLS Inspection
โซลูชัน Versa Network11 UTM นี้ยังมาพร้อมกับความสามารถด้านการถอดรหัส Secure Sockets Layer (SSL) ซึ่งเป็นเทคโนโลยีมาตรฐานในการทำให้การเชื่อมต่อ Internet มีความปลอดภัยและปกป้องข้อมูลที่มีความสำคัญสูงได้ และยังรองรับการถอดรหัส Transport Layer Security (TLS) ซึ่งเป็นเทคโนโลยีใหม่ที่ปลอดภัยยิ่งขึ้น ทำให้สามารถเปิดใช้งานเพื่อควบคุม Application, Security, Content และการทำ Compliance สำหรับข้อมูลที่ถูกเข้ารหัสได้
ความสามารถด้าน SSL และ TLS นี้รองรับการถอดรหัสของ Application ที่ถูกออกแบบมาโดยเฉพาะอย่างเช่น SMTP, HTTPS, SSH และ Traffic รูปแบบอื่นๆ ได้ แนวทางดังกล่าวนี้จะทำให้การควบคุม Public Key และ Private Key ถูกจัดการผ่าน RBAC ได้อย่างเหมาะสม ทำให้มั่นใจได้ว่ามีการบริหารจัดการ Profile สำหรับการถอดรหัสข้อมูลที่เหมาะสม